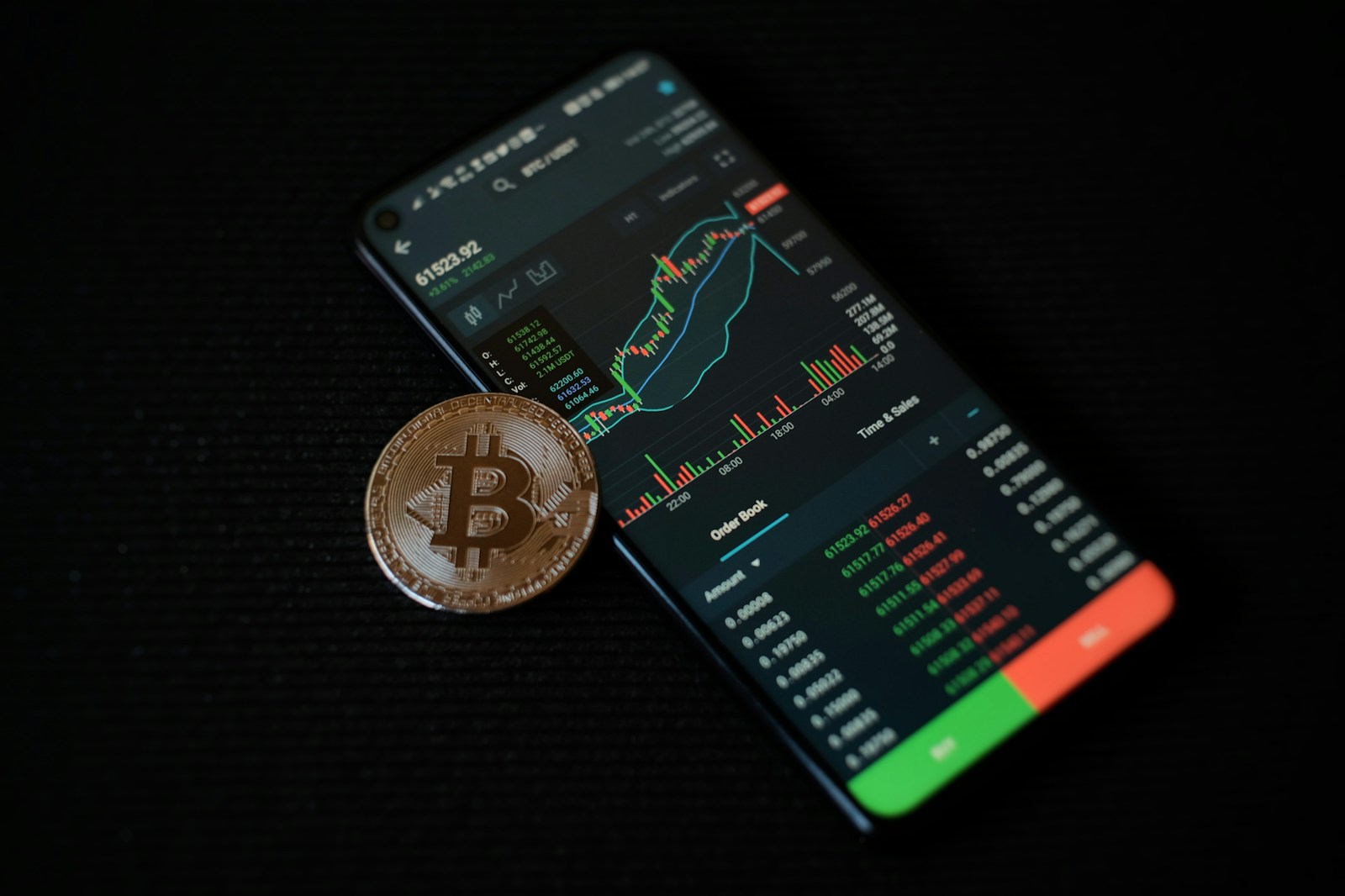
Mobile wallet security – protecting crypto on phones
Use biometric authentication and strong PINs immediately. Devices equipped with fingerprint scanners or facial recognition reduce unauthorized access risks significantly. According to recent data, apps employing biometrics report 40% fewer…